If your employer has organizational policies restricting access from unauthorized locations, it creates policy breach issues. But I will try to answer this question in good faith.
Accessing your site’s system without VPN
Virtually all websites record your IP address when you make requests. Consequently, when you visit a website, your account details and the IP address used for login are visible to them.
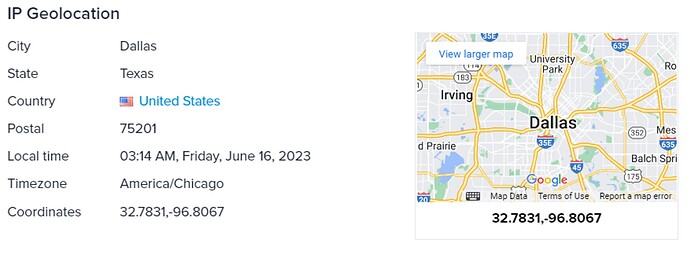
If you look up your IP address on IPinfo.io, you will get your IP geolocation information.
You can see the city, region and country from the IP address.
In cases where companies implement location access restrictions, requests originating from non-authorized areas (e.g., countries, regions or cities) may be denied by utilizing IP Geolocation data. This occurs because the user’s position is detected by determining their IP address’ location.
In some cases, they may not immediately block your access, but they can run regular audits by looking up the IP addresses you have used to access your account.
Accessing your site’s system with VPN
A VPN can change your IP location to any place where they supposedly have a server in. So, if you are in Japan and you are using a VPN service, you can pass your traffic from their server in the UK. From the VPN IP address, most of the time, it will look like it is based in the server location.
I am using a VPN that has a server based in Dallas; here is what IPinfo has to say about that IP address’ location:
Organizations can identify VPN usage
Organizations can easily detect VPN IP addresses using our privacy detection API. For example https://ipinfo.io/212.102.40.74
Your organization can use our IP privacy data to detect whether you are using a VPN or not. Based on this information they can restrict your access to the site, or they can detect your VPN usage when they run traffic log audits.
Another issue is that if you are using a company device (laptop, mobile phone etc.) your company can have root access to them. They can run IP geolocation calls from your devices that bypass your VPN software to find our your real IP geolocation. Sometimes root access like this allows organization to see the GPS-backed geolocation information of the device.