Strengthen your account security with ABAC powered with IPinfo’s IP data
In access control policies, RBAC (Role-Based Access Control) has been widely used to regulate user permissions and authorize access to particular resources. However, as cybersecurity attacks become more sophisticated and to meet the complexities of global and distributed businesses, the access control mechanism needs to evolve. Access control policies need to move beyond the one-dimensional access policies of RBAC.
From RBAC emerges ABAC
While RBAC usually only considers only criteria, the “Role”, ABAC or Attribute Based Access Control (ABAC) goes beyond that and incorporates multiple attributes beyond just the role attribute. ABAC can include the following attributes:
- Organization-assigned user attributes (Role, department, clearance level etc.)
- Resource attributes (resource sensitivity, resource type etc.)
- IP data attributes
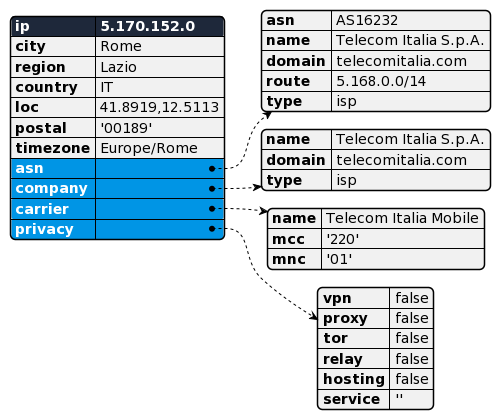
- Geolocation (city, country, continent, timezone etc.)
- Connection information (Connection type, AS of the IP, carrier type etc.)
- Anonymous IP information (VPN usage - whitelist/blocklist, TOR access, relays etc.)
Using IP data in ABAC
IP data plays a very important role in ABAC. The amount of meta information that can be extracted from IP addresses while accessing resources makes IP data-driven ABAC policies much more robust and effective. Moreover, the meta information associated with IP addresses is very difficult to imitate.
More information = Stronger access security
Let’s do an exercise on access control policies from an organizational perspective.
- Your HR team works from the office in Dallas, TX.
- Your engineering team in Australia typically works during the AEST work hours.
- You have provided company phones to your sales team in France through the telecom company Orange.
- You recommend that your remote workers use the VPN service NordVPN, and you do not permit access from any other VPN or anonymous IP address connections to your resources.
As you can see that you have identified a few practical attributes for your hypothetical organization. So, using IPinfo’s data, you can answer all these questions and get concrete attributes that you can use to verify access to your resources.
- Identify the city of the IP address → IPinfo IP to Geolocation data
- Identify the timezone of an IP address → IPinfo IP to Geolocation data
- Identify carrier IPs and ASN of IP addresses → IPinfo IP to Carrier data and IPinfo ASN database
- Identify VPN usage for blacklisting/whitelisting → IPinfo IP to Privacy Detection API
Because this IP meta information is being supplied by IPinfo, it is extremely difficult to replicate the traits/attributes of an authorized account’s IP address. If any attacker wants to replicate all the attributes that we provide, they essentially have to get physical access to the authorized device!
So, IPinfo’s IP data can be considered the cornerstone of ABAC policies. It is dynamic, effective, and incorruptible.
If you are interested in learning more about access control, we highly recommend you to check out our blog: IP address data for access control
https://ipinfo.io/blog/ip-address-data-for-access-control/
IPinfo services referenced:
API
- IP to Geolocation API)
- IP to Company API
- IP to Privacy Detection API
- IP to ASN API
- IP to Mobile Carrier API
Database
- IP to Geolocation Database
- IP to Company Database
- IP to Privacy Detection Database
- IP to ASN Database
- IP to Mobile Carrier Database
Free / Open access services
Signup for a free account today, and get access to the following services: